Saving these files on the server and referring to them by absolute path requires you to have a server login, and does not work on agents. This plugin gives you an easy way to package up all a job's secret files and passwords and access them using a single environment variable during the build. Using the credential binding plugin is more convenient and more secure than leaving them in code or some other insecure place on disk. Create a bash file with the following script to know how to use the read command with a variable.
After running the script, the program will wait for the user input. When the user types the data and press enter, the data will be stored in the answer variable. The value of the answer variable will be printed later.
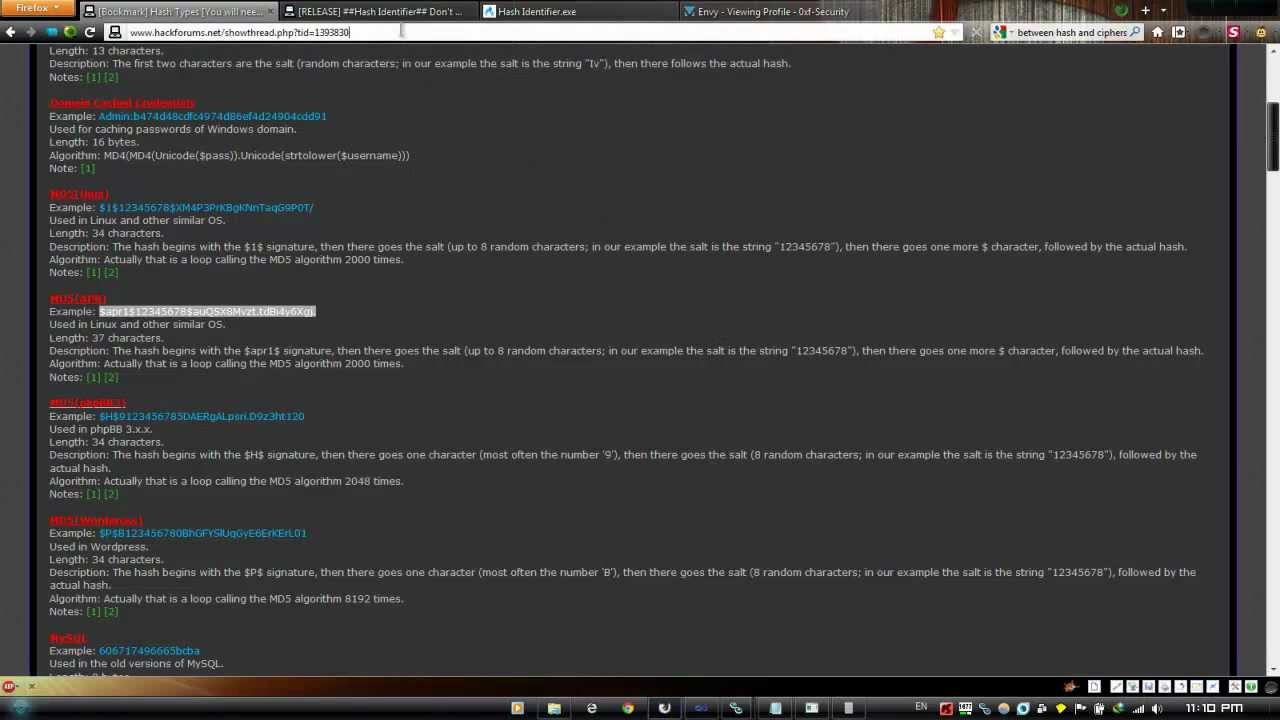
Resources available from the Apache HTTP server can be restricted to just the users listed in the files created by htpasswd. This program can only manage usernames and passwords stored in a flat-file. It can encrypt and display password information for use in other types of data stores, though.
Htpasswd is used to create and update the flat-files used to store usernames and password for basic authentication of HTTP users. To use, first go to the Credentials link and add items of type Secret file and/or Secret text. Now in a freestyle job, check the box Use secret text or file and add some variable bindings which will use your credentials.
The resulting environment variables can be accessed from shell script build steps and so on. (You probably want to start any shell script with set +x, or batch script with @echo off. JENKINS-14731). According to the hint, there is a configuration for a cron job on "/etc/cron.d/" that will help us complete this level. Cron is a program that will run a specific command or script at a specific time or intervals of time.
When I "cd" into the "/etc/cron.d/" folder and I ran "ls", I saw multiple file but I assumed that we have to look at the file named "cronjob_bandit22" since I have to get bandit22s password. I used "cat cronjob_bandit22" to see what the cron job is doing I saw that it is executing a bash script at every minute of every hour as explained by the stars in the beginning. Jenkins admins need to be aware of these privileges so they can properly design their infrastructure to minimize overexposure. Untrusted parties should also be prevented from configuring Jenkins jobs, and Jenkins should be carefully segmented with multiple numbers of job configurator users. These two scripts are very important for the system admin who regularly works with mail servers and somehow forgets to backup his system username and password! Let's say somehow we lost the usernames and passwords of the mail server.
In this case the admin has to manually create all the users and then change the passwords for all the users. Htpasswd returns a zero status ("true") if the username and password have been successfully added or updated in the passwdfile. After reading the man page of openssl I tried looking up the pattern -ign_eof by hitting the / key and typing the string.
I then tried to see what options are available for s_client by running openssl s_client -h which was not a valid command but I did get all of the options for s_client. I was then able to find the -ign_eof option the hint was talking about. As explained by the manual "-ign_eof" ignores the input eof. When we run the command below and I typed the password for bandit15 I received the new password.
The Linux read command provides you the option to prompt for user input. Once the user-provided input and hits enter, the command store provided input to a variable. Create a bash file with the following script to know how to use both –p and –s options together in the bash script. In this example, the username and password will be taken from the user and compared with the particular value to check the username and password are valid or not.
If you want your playbook to prompt the user for certain input, add a 'vars_prompt' section. Prompting the user for variables lets you avoid recording sensitive data like passwords. For example, if you use one playbook across multiple software releases, you could prompt for the particular release version.
The above script shows you the necessary steps to read credentials from a CSV file and create users on Linux. Keep in mind that the script it not very advanced and you can add a lot of improvements to it. Few things that you can add are error handling, help how to run the script as well as a way to run the script remotely. We will explain some of those in one of our future posts.
Validating a user is very straight-forward, as you can use id command with option -u or read /etc/passwd (using 'grep' command) file to do so (Read about /etc/passwd file format here). If the exit status is "0", then it's a valid user, else it's not. For those who are new to bash scripting- Exit status can be checked using echo $?. Taking input from the user is a common task for any programming language. You can take input from a user in bash script in multiple ways. A read command is used in the bash script to take data from the user.
Single or multiple data can be taken in bash script by applying different options of the read command. Some common uses of the read command are shown in this tutorial. Useradd command examplesIn some other Linux distributions, the useradd command may come with a slightly different version. I suggest you read your documentation, before using our instructions to create new user accounts in Linux. This Jenkinsfile can either be typed into the Jenkins job configuration web page by the job configurator user, or pushed into the code repository ("pipeline-as-code").
Like other tools, Jenkins needs to interface with a myriad of systems and applications throughout DevOps environments. The read command provides the silent mode option with "-s" to hide the input characters from the screen. Let's create a sample script to take password input from the user. To store the password files, I have created a directory at /home/vin/test/passwords. Here is how I set up my passwords directory for everyone but the user who owns it. By default, Docker looks for the native binary on each of the platforms, i.e. "osxkeychain" on macOS, "wincred" on windows, and "pass" on Linux.
A special case is that on Linux, Docker will fall back to the "secretservice" binary if it cannot find the "pass" binary. If none of these binaries are present, it stores the credentials (i.e. password) in base64 encoding in the config files described above. This manual describes the mechanisms Git uses to request these credentials, as well as some features to avoid inputting these credentials repeatedly. Echo -e means echo without carriage breaks at the end of the line.
So this echo command will spit out the password, a return and then the password again. We pipe that output to the passwd command followed by the $username variable taken in step 2. We all are aware of the most popular command called 'useradd' or 'adduser' in Linux. There are times when a Linux System Administrator is asked to create user accounts on Linux with some specific properties, limitations, or comments. The domain parameter is used to partition certain credentials. Each credential's domain is really defining an identity type.
The domain specifications define how to determine which identity might be valid against any specific service. The JENKINS_HOME directories allow anyone to decrypt and expose all secrets used by Jenkins. Jenkins supports building CD pipelines through either a web UI or a scripted Jenkinsfile committed to source control. It is always recommended to use encrypted passwords in Linux bash shell scripts.
Typically, in bash shell script we may need password for remote user while connecting to remote system, ftp user and proxy user etc. In this article, we will cover how to encrypt password using openssl command and then will see how this encrypted password can be used in bash shell script. OptionPurpose-pIt is used to provide a helping message for the user before the input prompt.-s It is used to take invisible input from the user. This option is used to take a password or secret data. -t It is used to set time in seconds to wait for taking input from the user.-nIt is used to set the limit of input characters.
Hello all, I am i am trying to read username password. Bassicaly, i have file called sidlist and it has my database name, username and password.... Db1, user1, pass1 db2, user2, pass2 db3, user3, pass4 but i dont know how to make it work, until i get...
As a System administrator, creating users on multiple servers maybe something that you would do on a daily basis. It maybe an easy task to create a user on single server but imagine that you need to add a user on 100+ different Linux servers. The store command takes a JSON payload from the standard input. That payload carries the server address, to identify the credential, the user name, and either a password or an identity token. If the GIT_ASKPASS environment variable is set, the program specified by the variable is invoked. A suitable prompt is provided to the program on the command line, and the user's input is read from its standard output.
This level seems to be similar as the 2 before this one. The configuration for the cron job is in "etc/cron.d/" and the name of the file is "cronjob_bandit24". The cron job is running a script named "cronjob_bandit24" in the "/usr/bin/" directory. After moving into that directory and reading the script I see that the script runs and then deletes all of the scrips in the "/var/spool/bandi24" folder. In the second hint they state that I have to write my own script and I have to put it in that folder for when it executes. Use a 'least exposure principle' to limit credentials exposure in the Jenkins pipeline.
Make sure credentials are visible to the minimum essential number of users and processes. It's these secrets that are increasingly sought out by attackers to carry out cyber security attacks – and this research demonstrates how. By default, your created users will likely have the default login shell bin/bash or bin/sh, which will be defined in /etc/default/useradd. In this tutorial, you will learn, how to prompt for user input in a shell script. Also, help you with accepting passwords from users in hidden characters. To create a password file in Linux, I am using the echo command by redirecting its output to a file to write the password for a specific user quickly.
In the below example, It will create a password file system.pw for the user SYSTEM and storing the password VINISH. For the below example, I am creating a single file to store the password for each user. Suppose you want to store the password for three users then you need to create three files. For example, the filename will be the username, and it will save the password for that user only.
Because there could be multiple users on the system, it is, therefore, necessary to manage their authentication. Authentication is primarily handled with passwords and public keys. One of the many tools available we use to set up passwords is thepasswd command. The array variable can be declared and initialized by using the read command.
Create a bash file with the following script to know how to create and initialize an array by using the read command. Next, all elements of the array, the first element of the array, the first two elements, and the last element of the array will be printed. The $REPLY variable is used to read the input taken from the user by the read command without variable. Create a bash file with the following script to know how to use the read command without any variable. The read command offers the -s tag to hide sensitive information input. A common use case is to combine -s with the -p tag to create a password prompt.
The Bash read command comes with many options to control the user input. Some options do not require additional parameters, while others have mandatory parameters. Thereadcommand takes the user input and splits the string into fields, assigning each new word to an argument. If there are fewer variables than words, read stores the remaining terms into the final variable.
Sometimes the nature of the data is such that it would not be ideal for it to be stored in peoples command histories etc. In these circumstances it is best to read the data during script execution. If you use file-based user authentication, the elasticsearch-users command enables you to add and remove users, assign user roles, and manage passwords per node. I tried to log in with both passwords but they did not work. When I logged into the profile I saw the data.txt file and when I read it a bunch of lines came up and it looked like all of the lines had the same structure.
It was a word followed by some spaces and then a possible password. The hint was that the password is next to the word millionth, so I used the command below to read the file and then grep the word millionth. The '-c' option adds the extra information about the user and the '-U' argument creates/adds a group with the same name as the user. Jenkins administrators sometimes leave the '# of executors' setting in the Jenkins configure system page at its default state and create a larger attack surface for malicious Jenkins users.
This allows job configurators/Jenkinsfile committers to elevate their privileges on the Jenkins master. The username/password combinations are configured directly to the auth method using the users/ path. This method cannot read usernames and passwords from an external source. The below shell script read_password.sh will read the password from the file system.pw using the cat command and will store the password into the variable system_pw.
We are saved by the fact that echo is a builtin, and a process will never be created. So, if you are able to otherwise secure your environment variables, this approach is safe. The downside is that it appears unsafe, because $STEP_CA_PASSWORD is still getting substituted into something that certainly looks like it's a command. If we don't want the characters to be displayed on the screen, we need to use the -s option with the read command. The linux read command is used to take a user input from the command line.